What Is Not a Terrorist Method of Surveillance? Surveillance plays a crucial role in maintaining national security and preventing acts of terrorism. As technology continues to advance, various methods of surveillance have emerged, some of which have been associated with terrorist activities. However, it is equally important to explore what is not a terrorist method of surveillance.
In this article, we will delve into What Is Not a Terrorist Method of Surveillance?, highlighting their significance in different contexts and their impact on privacy and security.
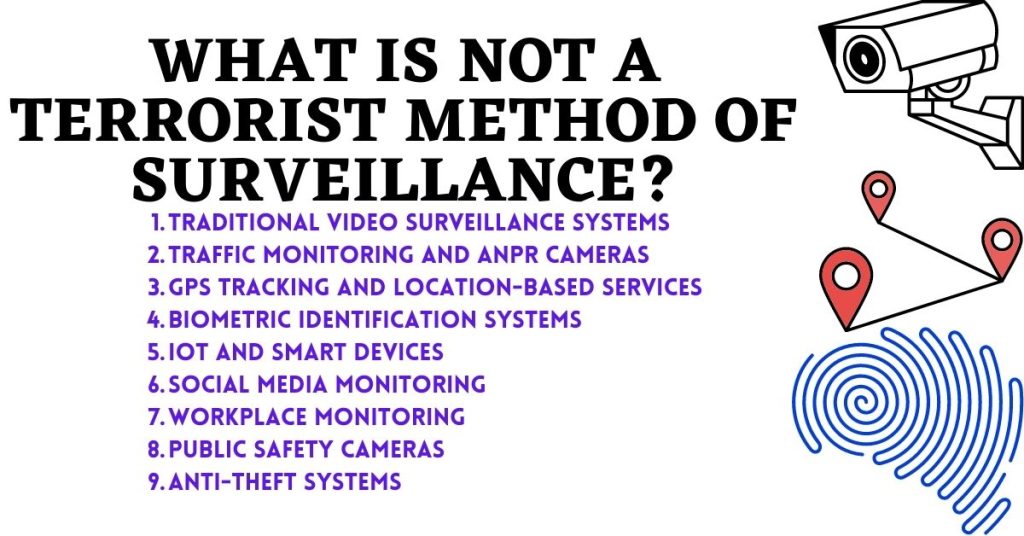
What are the Non Terrorist Methods of Surveillance?
Surveillance is the systematic monitoring of individuals, groups, or environments to gather information. While terrorists may exploit surveillance techniques for their malicious activities, it is essential to acknowledge that surveillance itself is not inherently terrorist. Many surveillance methods are employed by governments, organizations, and individuals for legitimate purposes such as public safety, crime prevention, and enhancing efficiency. Let’s explore some non-terrorist methods of surveillance that are commonly used today.
1. Traditional Video Surveillance Systems
One of the most recognizable forms of surveillance is the use of traditional video surveillance systems. Closed-circuit television (CCTV) cameras are strategically placed in public areas, providing a visual record of events. These cameras are instrumental in deterring criminal activities, assisting law enforcement investigations, and ensuring public safety. While they can be misused, their primary purpose is to protect citizens and maintain order rather than facilitate acts of terrorism.
2. Traffic Monitoring and ANPR Cameras
Traffic monitoring systems and Automatic Number Plate Recognition (ANPR) cameras have become increasingly prevalent in modern cities. These technologies help manage traffic flow, enforce traffic laws, and identify vehicles involved in crimes. By capturing license plate information, these surveillance methods aid law enforcement agencies in locating stolen vehicles, tracking suspicious activities, and ensuring road safety. Their primary focus is to maintain law and order rather than perpetrate acts of terrorism.
3. GPS Tracking and Location-Based Services
GPS tracking technology has revolutionized navigation and location-based services. While some individuals may have concerns about privacy, it is crucial to recognize the legitimate uses of GPS tracking for personal safety, asset tracking, and emergency services. Law enforcement agencies employ this technology to monitor parolees and track individuals suspected of criminal activities. It helps maintain public safety rather than support terrorist endeavors.
Read Now: What To Say When Claiming Phone Insurance? Total Guide
4. Biometric Identification Systems
Biometric identification systems utilize unique physical or behavioral characteristics, such as fingerprints or facial recognition, to verify an individual’s identity. These systems have various applications, including access control, border security, and law enforcement investigations. By accurately identifying individuals, biometric surveillance methods aid in preventing unauthorized access, enhancing security, and assisting in criminal investigations. Their focus is on maintaining security rather than promoting terrorism.
5. IoT and Smart Devices
The Internet of Things (IoT) has connected numerous devices, enabling seamless communication and data exchange. While concerns about IoT security exist, it is essential to understand the positive aspects of these interconnected devices. Smart home systems, for example, provide convenience, energy efficiency, and enhanced security. By monitoring and controlling various aspects of a home, these devices offer homeowners peace of mind and a safer living environment.
6. Social Media Monitoring
Social media has become an integral part of modern life, with billions of people sharing their thoughts, opinions, and experiences online. Governments and law enforcement agencies utilize social media monitoring to gather intelligence, detect potential threats, and prevent criminal activities. By analyzing public posts and profiles, they can identify individuals of interest, investigate potential security breaches, and ensure public safety. Social media monitoring aims to protect citizens rather than promote terrorism.
Read Now: What Is One Responsibility That Is Only For United States Citizens?
7. Workplace Monitoring
Workplace monitoring refers to the surveillance techniques employed by employers to ensure productivity, maintain security, and prevent unauthorized activities. This can include video surveillance, computer monitoring, and email tracking. While it is essential to strike a balance between privacy and security, workplace monitoring primarily aims to protect sensitive information, prevent fraud, and create a safe working environment. Its purpose is not to facilitate terrorist acts but to maintain integrity within organizations.
8. Public Safety Cameras
Public safety cameras are installed in various locations, such as streets, parks, and public buildings, to monitor activities and respond to emergencies promptly. These cameras act as a deterrent to crime, aid in identifying perpetrators, and provide valuable evidence for investigations. The primary objective of public safety cameras is to ensure the well-being of citizens and maintain order, making them non-terrorist surveillance tools.
9. Anti-Theft Systems
Anti-theft systems are commonly used in retail stores, protecting merchandise from theft and reducing losses. These systems include security tags, surveillance cameras, and alarms. While their purpose is to prevent theft and maintain the security of commercial establishments, they are not intended for terrorist activities. Anti-theft systems contribute to the overall safety of businesses and customers.
Read Now: How To Dispute Parking Ticket in Toronto
Conclusion
In conclusion, while surveillance techniques can be exploited by terrorists, it is important to recognize the multitude of non-terrorist surveillance methods that are essential for maintaining security, preventing crime, and ensuring public safety. Traditional video surveillance, traffic monitoring, GPS tracking, biometric identification systems, IoT devices, social media monitoring, workplace surveillance, public safety cameras, and anti-theft systems all serve legitimate purposes. By understanding their intended use and potential benefits, we can strike a balance between privacy and security, fostering a safer society.
FAQs
No, surveillance methods are employed for various purposes, including public safety, crime prevention, and enhancing efficiency.
Traditional video surveillance systems deter criminal activities, assist in law enforcement investigations, and ensure public safety.
Yes, social media monitoring assists in gathering intelligence, detecting potential threats, and ensuring public safety.
Michael C Vang is a passionate blogger. He has been blogging since 2013 on a variety of topics. He is committed to creating informative and engaging content that helps readers learn more about everything.